This Scary New Phishing Attack Is Very Hard To Detect
You need to know about a new phishing attack vector just reported. It utilizes a new technique that’s just plain nasty.
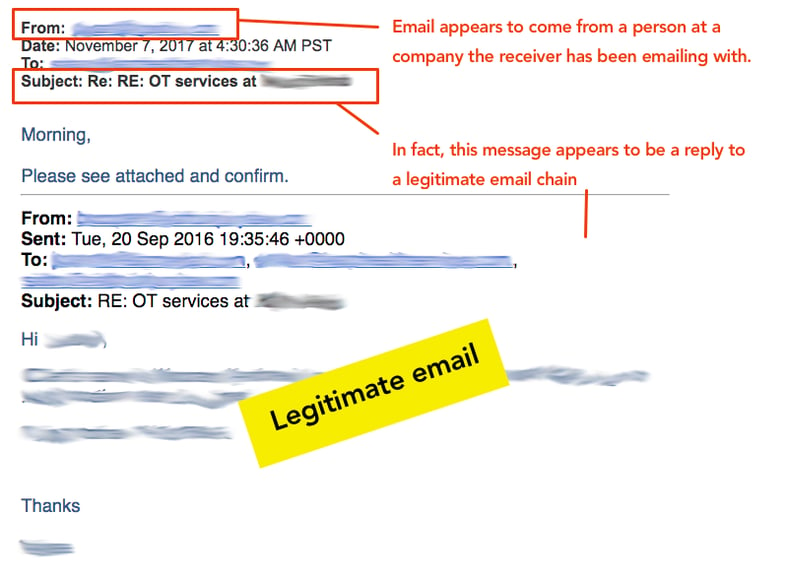
This week, users at one of their customers began receiving emails from known contacts they had at another organization. In the screenshot below you can see that at least one of the emails appeared to be a reply to an existing email thread, where users at the two organizations had been emailing back and forth.
The new message was noticeably short — “Morning, please see attached and confirm” (you probably see where this is going) — but in the context of the email chain it was very convincing. The email appears to come from a person at a company the receiver has been emailing with, and this message appears to be a reply to a legit email chain. Yikes.
The aim was to have the user open the Word attachment, and follow instructions to enable macros.
Technical background of the attack
The user on the other end had been infected with a new variant of Ursnif, one of the most active and widespread banking trojans in the world.
Investigation showed that the Word doc the user downloaded contained a macro that, when activated, launched PowerShell script designed to download the Ursnif payload.
Ursnif is a powerful trojan with a lot of features like stealing victim credentials in a variety of ways via man-in-the-browser attacks, keylogging, screenshot capture, etc.
It looks like the evil masterminds behind Ursnif are now taking it one step further and use the compromised email accounts of its victims to spread the infection like a worm.
The moral is: NEVER OPEN Word Docs unles syou know exactly what they are and what they contain.
Do not be curious and open them just to “see” what they are. Ask you IT person at Command Com for help any time you suspect an email is malicious and let us look at each email to determine if it is safe or not.
 D5 Creation
D5 Creation